
Researchers find serious flaw in WordPress Real-Time Find and Replace plugin
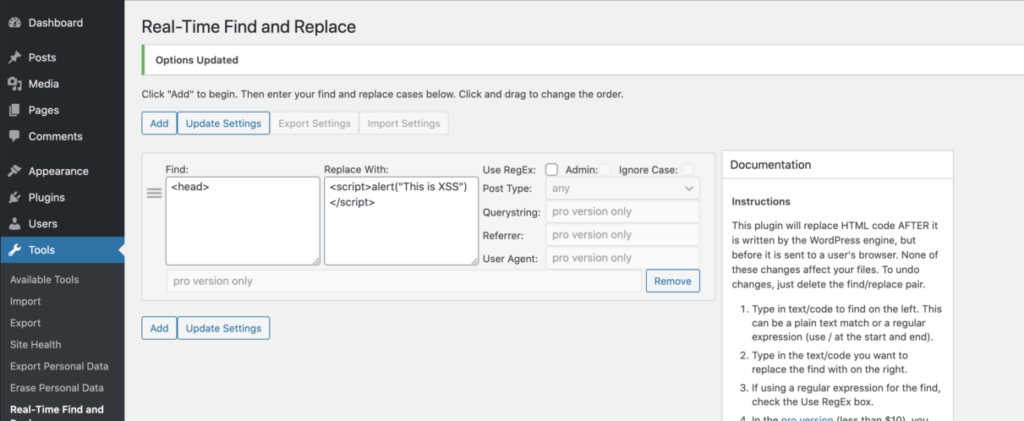
Recently, a critical vulnerability was discovered in old versions of the Real-Time Find and Replace WordPress plugin that could allow hackers to inject malicious JavaScript into your site and create multiple admin accounts.
On April 22, researchers at Wordfence discovered a Cross-Site Request Forgery (CSRF) vulnerability in the Real-Time Find and Replace plugin that is currently being used by more than 100,000 WordPress site owners.
The Real-Time Find and Replace plugin claims to provide the functionality to dynamically replace code and text on WordPress sites with the new content without permanently changing the source content. It also offers filtering options, setting export/import functionality, and the ability to modify admin pages.
The CSRF vulnerability present in the plugin leads to a Stored Cross-Site Scripting (Stored XSS) attack. Wherein, an attacker could take advantage of a vulnerable website and inject malicious JavaScript code on every page. This injected malicious code then gets automatically executed anytime a user tries to access the original site content.
Further, the malicious code could be used by an attacker to inject a new admin account, steal session cookies, and even redirect users to another malicious site.
According to the report published yesterday by Wordfence researcher, the vulnerability is considered as a high-severity security issue with a CVSS score of 8.8.
“We reached out to the plugin developer on April 22, 2020, and they released a patch just a few hours after we disclosed the vulnerability to them,” says the report.
Wordfence recommends the plugin users to immediately update the plugin to its fully patched version 4.0.2 to secure their websites.

It can be seen in a above image that even after the developer’s prompt response for issuing patches, more than 78% of the 100,000+ active users are still using old versions of the plugin leaving their websites vulnerable to CSRF and Stored XSS.
Also Read: WordPress SEO Plugin RankMath Fixes Critical Security Vulnerability

