
Ninja Forms WordPress plugin fixes a high-severity vulnerability
A high-severity Cross-Site Request Forgery (CSRF) vulnerability was discovered in the WordPress Form plugin Ninja Forms that could
allow hackers to upload or replace existing contact forms with the malicious version and even gain full administrator access.
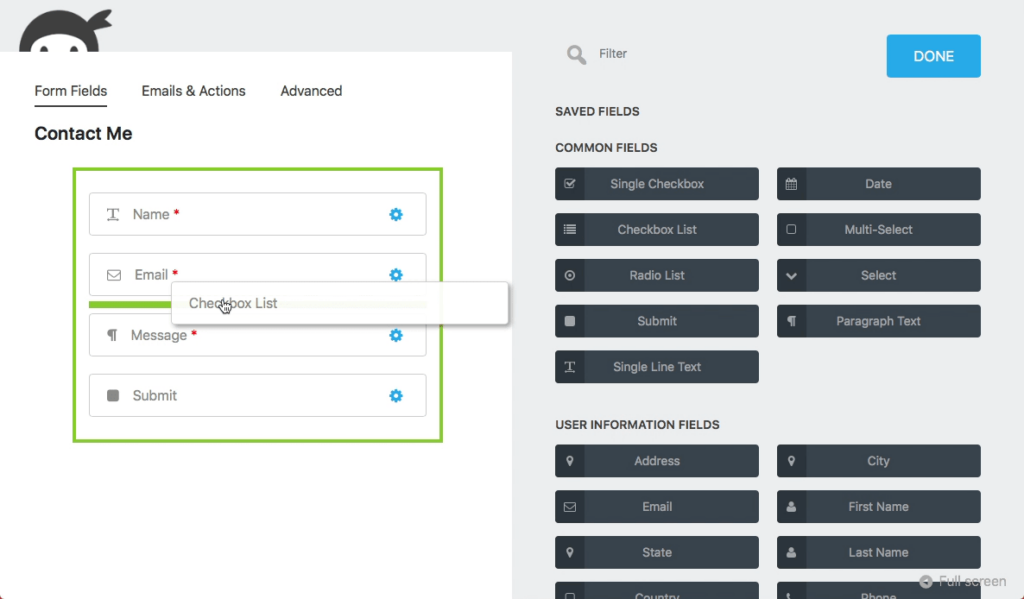
Ninja Forms is a drag and drop form builder for WordPress that claims to provide an interface for its users to build complex forms and integrate on their websites. The plugin also offer optional forms for accepting payments via PayPal, Stripe, and more.
It is currently used by more than 1 million website owners and any of these websites could be easily hacked if their Ninja Forms plugin is not updated.
The vulnerable versions of the Ninja Forms WordPress plugin are lower than v3.4.24.2.
Threat Intelligence team at Wordfence discovered this Cross-Site Request Forgery (CSRF) vulnerability in the Ninja forms’ “Legacy” mode with the CVSS Score of 8.8 (High).
As part of the Legacy mode feature, “it adds several AJAX functions which appear to be intended to import forms and fields between the “legacy” mode and the default mode. While all of these functions used capability checks, two of the functions failed to check nonces, which are used to verify that a request was intentionally sent by a legitimate user,” Wordfence report describes.
Read Also: This is why Astra Security is a must have security plugin
By exploiting this vulnerability, hackers can easily spoof a request using the administrator’s session and import a form containing malicious JavaScript into the site.
“Depending on where the JavaScript was placed in the imported form, it could be executed in a victim’s browser whenever they visited a page containing the form, whenever an Administrator visited the plugin’s Import/Export page, or whenever an Administrator attempted to edit any of the form’s fields,” the experts said.
It could also further allow hackers to perform Cross-site Scripting (XSS) attacks and take over the complete site access.
Here’s a vulnerability disclosure timeline provided by Wordfence:
- April 27, 2020 19:00 UTC – Wordfence Threat Intelligence discovers and analyzes vulnerability.
- April 27, 2020 19:24 UTC – Full vulnerability disclosure sent to the plugin’s developer as per their Responsible Security Disclosure Policy.
- April 27, 2020 20:27 UTC – Wordfence received a response from the dev team that the patched should be available the next day.
- April 28, 2020 19:00 UTC – Patched version of the plugin released (v3.4.24.2)
On 27th April, Wordfence’s research team shared the discovery report with Ninja Forms, and a day later, on 28th April, the developers at Ninja Forms issued an updated version of the plugin by fixing their existing code.
“One of the reasons this plugin was patched so quickly was because the plugin’s team maintains a Responsible Security Disclosure Policy, often referred to as a Vulnerability Disclosure Policy,” report by Wordfence further added.
If you are one of the 1 Million+ customers of Ninja Forms using their plugin for your WordPress, it is highly recommended that you should update the plugin to the fully patched version 3.4.24.2.
Source: Wordfence

